As organizations become more reliant on digital communication, the risk of cyber attacks increases. One type of attack that poses a significant threat to network security is ping spoofing. In this blog post, we will explain what ping spoofing is, how it works, the different types of attacks, the risks associated with it, and steps to prevent it.
Table of Contents
What is Ping Spoofing ?
Ping spoofing is a type of network attack where an attacker sends packets to a target device with a forged source IP address. The purpose of this attack is to deceive the target device into believing that the packets are coming from a trusted source. Once the attacker gains access, they can perform various malicious activities, including stealing sensitive data or controlling the device.
Ping spoofing is a technique that involves sending a forged ping message to a computer, with the goal of disguising the source of the ping and making it appear as if it is coming from a different computer or device. This technique can be used for a variety of purposes, including network testing and troubleshooting, as well as malicious activities such as distributed denial of service (DDoS) attacks and network intrusion.
Many people wonder What is Ping spoofing! Spoofing is basically a type of attack on a server. With this attack, the server may not be able to serve genuine requests.
This attack can be classified under a DOS (Denial of Service) attack and in the cloud security world.
The umbrella acronym is DDOS (Distributed Denial of Service) in which there are many attacking systems over the distributed network.
Under DDOS attacks the target system (e.g web server) will be flooded with fake requests increasing the server load and when a genuine request from a real user comes, the server is either very slow to respond or may not be able to respond at all due to the massive load.
With this type of attack, businesses can be hurt especially if it’s an online business like an eCommerce website or any service which is highly dependent on its online users. Thus it becomes important to have risk mitigation plans and tools to be secure from these types of attacks.
How Ping Spoofing Works
Ping spoofing works by manipulating the source IP address of packets sent to a target device. The attacker can use various techniques to conceal their identity, such as IP address spoofing, MAC address spoofing, and DNS spoofing. By doing this, they can trick the target device into believing that the packets are coming from a legitimate source and gain unauthorized access to the network.
To perform ping spoofing, an attacker may use a tool that allows them to forge the source IP address in the ping message. The attacker can then send the forged ping message to a target computer, which will respond to the message as if it were a legitimate request. The attacker can then capture the response and use it to gather information about the target network or launch further attacks.
Types of Ping Spoofing
There are different types of ping spoofing attacks, including blind spoofing, non-blind spoofing, and man-in-the-middle (MITM) spoofing. Blind spoofing is when the attacker sends packets to the target device without receiving any responses. Non-blind spoofing is when the attacker sends packets to the target device and receives responses from it. MITM spoofing is when the attacker intercepts and modifies the communication between two devices on the network.
Risks Associated with Ping Spoofing
Ping spoofing can lead to several risks, including data theft, system damage, and unauthorized access. Attackers can use ping spoofing to steal sensitive information, such as passwords, credit card numbers, or other confidential data. They can also use it to gain control of the target device or disrupt the network’s normal operation.
How to Prevent Ping Spoofing
It is important to note that ping spoofing is generally considered a security vulnerability and can be mitigated through the use of appropriate network security measures. This includes properly configuring firewalls and intrusion detection and prevention systems to detect and block forged ping messages, as well as regularly updating software and operating systems to address known vulnerabilities that may be exploited for ping spoofing.
There are several steps that organizations can take to prevent ping spoofing attacks:
- Use an intrusion detection system (IDS) to detect spoofed packets: IDS can help identify ping spoofing attacks by analyzing network traffic and detecting unusual patterns.
- Configure routers and firewalls to block spoofed packets: Routers and firewalls can be configured to block packets with spoofed source IP addresses.
- Utilize encryption to protect against sniffing and eavesdropping attacks: Encryption can prevent attackers from intercepting and reading network traffic.
- Use access control lists (ACLs) to restrict access to sensitive network resources: ACLs can limit access to sensitive resources and prevent unauthorized access.
- Monitor network traffic for unusual activity: Network administrators should regularly monitor network traffic for any unusual activity that may indicate a ping spoofing attack.
- Educate employees on how to recognize and report suspicious behavior: Employees should be trained to recognize suspicious behavior and report any suspicious activity to network administrators.
Examples of Ping Spoofing ?
Here are a few examples of how ping spoofing might be used:
- Network testing and troubleshooting: An administrator might use ping spoofing to test the reachability of a particular device on a network, or to diagnose connectivity issues between devices.
- DDoS attacks: An attacker could use ping spoofing to flood a target device or network with forged ping messages, overwhelming its resources and causing it to become unavailable to legitimate users.
- Network intrusion: An attacker could use ping spoofing to gather information about a target network, such as which devices are online and how they are configured. This information could be used to identify vulnerabilities that could be exploited to gain unauthorized access to the network.
- Phishing attacks: An attacker could use ping spoofing to send a forged ping message that appears to be from a trusted source, in an attempt to trick a victim into revealing sensitive information or installing malicious software.
It’s important to note that ping spoofing is generally considered a security vulnerability, and appropriate measures should be taken to prevent it. This includes configuring firewalls and intrusion detection and prevention systems to detect and block forged ping messages, as well as regularly updating software and operating systems to address known vulnerabilities that could be exploited for ping spoofing.
Ping in Networking
Ping in computer networking is the time it takes to send a packet from one system to another. If you have a good network connection you will see less ping and if you have a bad network connection you will see high ping.
What is Ping Spoofing in Minecraft Game
Ping spoofing in Minecraft game refers to a malicious technique used by some players to manipulate their network connection and create an unfair advantage over other players. In Minecraft, a player’s ping is the time it takes for their device to communicate with the game server and receive a response. Players with a lower ping can often perform actions more quickly and accurately than those with a higher ping.
Ping spoofing in Minecraft involves manipulating the player’s ping time to appear lower than it actually is. This is achieved by sending false ping packets to the game server, which tricks the server into believing that the player’s device is located closer to the server than it actually is. As a result, the server sends game data more quickly to the player’s device, giving them an unfair advantage over other players.
Ping spoofing in Minecraft is considered cheating and is not allowed by the game’s terms of service. Players who are caught using ping spoofing techniques can face penalties such as temporary or permanent bans from the game.
Due to the lagging, they get an unfair advantage to attack the opponent and win games unfairly.
What is a Ping Spoofer?
Ping Spoofer is a gamer or a participant in a network resource-oriented game or tool who will manipulate their ping value to misinform the other network participants.
A ping spoofer is a remote program service that sends high ping packets as If it originates from a user’s computer system address. This system that gets the package sends out ping responses to the servers, as well as if you be successful in getting this number high sufficient, the webserver prospers in receiving hundreds, otherwise hundreds of not-requested replies from different sources. This is successful in overloading the network and also considering that these high packages are not sent out from your address, the webserver that’s under attack will not have the ability to blacklist you.
That’s why most web servers and also cloud gamers utilize ping spoof detectors to recognize which players are ping spoofing.
Detecting Ping Spoofing
Detecting ping spoofing is hard, as the manipulators increase the ping, by intentionally delaying sending the keep-alive packets.
Probably watch a suspected spoofer’s ping time over a period and see if the ping is abnormal may mean something is wrong. Check whether the sender data is lagging or not. If the data sent by the system is not lagging and it really consists of high ping data, then it is not detectable.
There are some tools like LagPoint available to check the latency of another server and it doesn’t rely on ping data only.
To prevent ping spoofing in Minecraft, game developers regularly update the game’s network security measures and implement anti-cheat systems to detect and prevent cheating. Additionally, players can report suspicious behavior to the game administrators for investigation.
FAQ
How to identify a Ping Spoofer?
if the ping is very unusual you can use ping spoofer detecter software to test if there are really network delays.
How to Ping Spoof in Minecraft?
Though this is not fair and might be banned, it involves manually changing the Ping value.
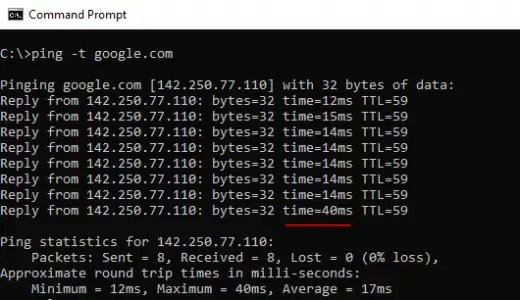
How to Check my Network Ping?
You can use the command on DOS prompt of PC e.g> ping -t google.com
Conclusion
Ping spoofing is a significant threat to network security. However, with the right measures, organizations can prevent these attacks from occurring. By using an IDS, configuring routers and firewalls, utilizing encryption, implementing ACLs, monitoring network traffic, and educating employees, organizations can protect their networks from ping spoofing attacks.
Also read: How to setup a minecraft server on Oracle Cloud
Next article: what is 192.168.1.1
more on technologies